Cybersecurity of the business environment is at least as important as physical protection of company’s assets.
In companies without automated update processes, software updates and upgrades, which frequently address security weaknesses, can be delayed by months. As a result, these companies have weaknesses in their IT environment that can be exploited by skilful attackers, even though a fix for the problem has been available for a while.
What is ISO 27001?
Effective and secure information management practices
ISO 27001 is an information security management standard. This international standard helps companies and organisations around the world establish and maintain the best possible information security management system (ISMS). This internationally recognised certificate, which is regularly audited by an independent auditor, demonstrates a continuous commitment to improving and protecting important digital assets.
Business benefits of having the system in place:
- Identifying and reducing security risks to the desired level;
- Improving business partnerships (increased confidentiality of exchanged information);
- Management of information security processes;
- Regular backups, off-site data backup, cyber security upgrade, mail server update with the latest patches, procurement of a public key certificate enabling the protection of multiple sub-domains (Wildcard certificate), etc.;
- Implemented final plan for the introduction of ISMS in the company.
ISO 27001 from the ISO/IEC 27000 family is one of the best known standards in the area of information security, and sets requirements for information security management systems (ISMS).
The company, with the support of external experts, implements a suitable information security management system – ISMS. ISMS implementation is a complex activity, which is carried out with the guidance of ISO/IEC 27003 standard and the use of project management software tools.
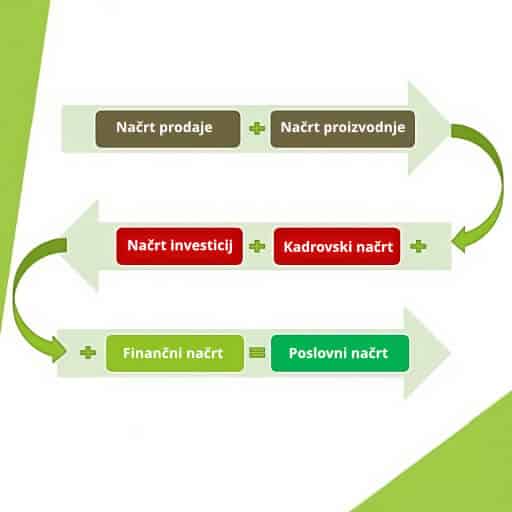
Implementation planning is divided into the following five phases:
- Phase: Obtaining management approval to start the ISMS implementation project.
- Phase: Defining the scope of the ISMS policy, scope boundaries and security policy.
- Phase: Analysis of information security requirements.
- Phase: Risk assessment and development of a safeguards proposal.
- Phase: Development of the final ISMS implementation plan.
What is ISO 27003?
ISO 27003:2017, with the full title ISO 27003:2017 Information technology — Security techniques — Information security management systems — Guidance, provides guidance for the implementation of ISO 27001 and meeting its detailed criteria. ISO 27003 is not a certificate. It is a basic guide and does not go into all the details of ISO 27001 implementation.
Compliance with ISO 27001 can be difficult for small businesses or organisations trying to obtain the certificate for the first time, so following the guidelines outlined in ISO 27003 is highly recommended to ensure success.
Our services:
- Security penetration testing.
- Proposal of measures for improving network security.
- Preparation of a blueprint (network security improvement plan).
- Assistance in preparing the terms of reference for a request for proposal (RFP).
- Assistance in obtaining quotations and selecting a provider.
- Assistance in getting ready to implement an ISMS in the company.
- Applying for the reimbursement of the ISO 27001 certification cost.
- Administrative management for the purpose of reporting and submitting reimbursement claims.
Are you ready to make a change and reduce your company's environmental impact?
We have the experience and expertise to help you achieve impact on all three pillars of sustainability.